Azure Key Vault provides a cloud service for managing keys, secrets, and certificates. In this key vault, developers are not needed to store security information in their code. It also reduces the chances of your application secrets being leaked due to the centralization of storage. Key Vault also enables you to securely store keys and secrets with the help of HSM’s (Hardware Security Modules). These HSMs are Federal Information Processing Standards (FIPS) 140-2 Level 2 validated. Also, the Key Vault provides details of all usage and access attempts of your stored data. This way you have a complete audit trail for any sort of compliance. Also it allows users to safeguard and control secrets and keys related to cryptography used by Cloud services and apps.
Types of Keys
There are two (2) types of keys.
- Soft Key
- Hard Key
Soft Key: This key is processed by Key Vault by software and is encrypted a key in an HSM called System key.
Hard key: This key is processed in the HSM, protected in one of the Key Vault HSM security worlds.
Key Vault Objects
Keys
Secrets
Certificates
Password for PFX files
Storage Account Access Keys
RSA Key: RSA Sizes 2048. 3072 & 4096
EC Key: P-256, P-384, P-521 and P-256K (SECP256K1)
Can generate and X.509 certificate and can manage life cycle management.
Note:
It does not issue or resell certificates from Public Cas but instead automates Life cycle management, enrollment and renewal of certificates from Public Cas.
Key Operations
These are the operation supported by Key Vault.
- Create
- Delete
- Update
- Restore
- Backup
- Get
- Import
- List
- List versions.
Creating Key Vault
Login to Azure Portal — https://portal.azure.com/
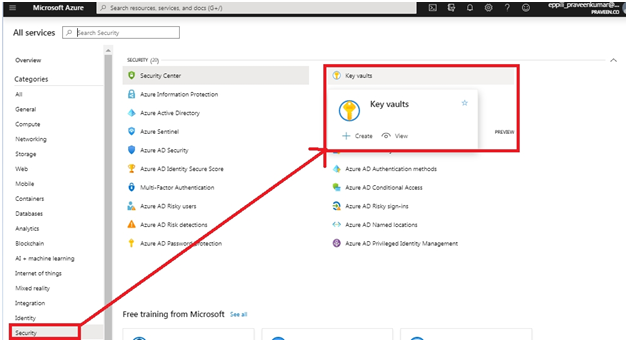
Go to services, in the security, Click on Key Vault.
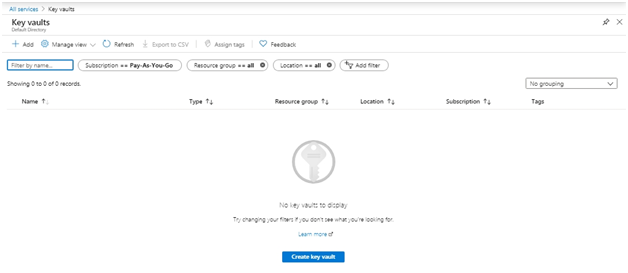
Now, Click on Create Key Vault.
Now enter the required information.
There are two pricing options available.
- Standard
- Premium (Support for HSM backed keys included)
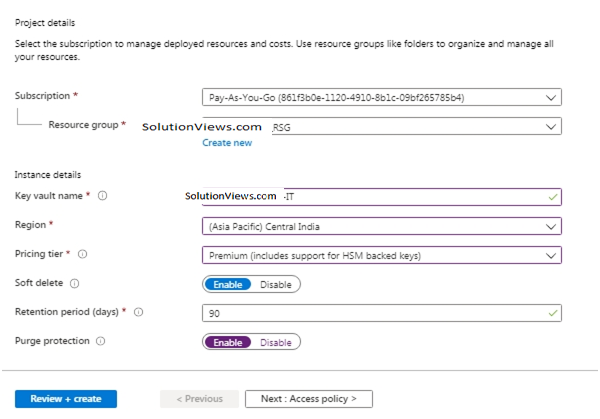
- Note: You can enable Purge Protection if you want, it will be disabled by default.
Do not directly click Review + create
Access Policy
Your code is able to get access tokens to get authentication to resources that support Azure AD authentication Using managed identities for Azure resources. But Azure AD authentication is not supported by All Azure services. Store the service credentials in Azure Key for using managed identities for Azure resources with those services and to access Key Vault for retrieving the credentials, use the VM’s managed identity.
First, we create a Key Vault and give our VM’s managed identity access to the Key Vault.
Now, go to AccessPolicy for enabling access to resource Manager, Azure VM, and Disk Encryption for Volume Encryption.
Also, your policies for Key Secrets & Certificates can be defined by you.
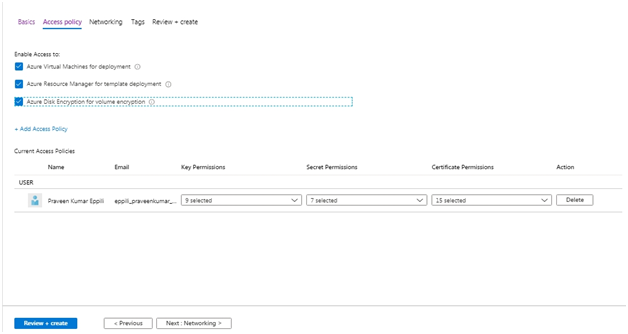
Moving forward with the default values.
Now, go to Networking.
Networking
You can access this Key Vault using Public IP addresses or service endpoints, or privately or private endpoints.
It can be chosen as per your requirements. For now, we will move forward with default settings
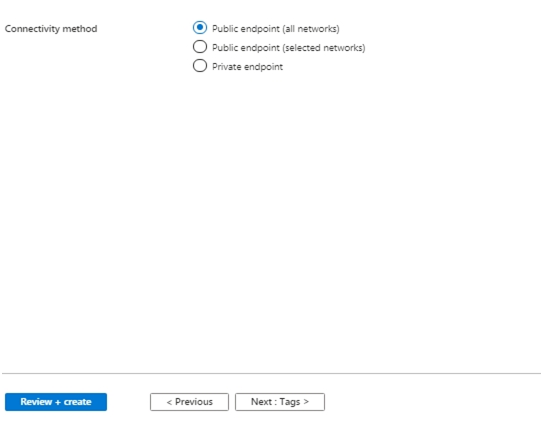
that are Public Endpoints (all networks).
Now, moving to Tags.
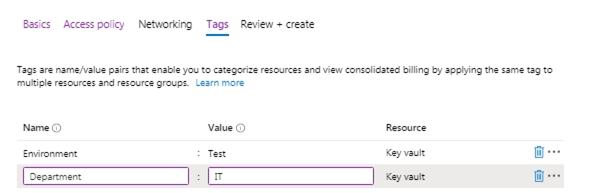
Enter Name & Value.
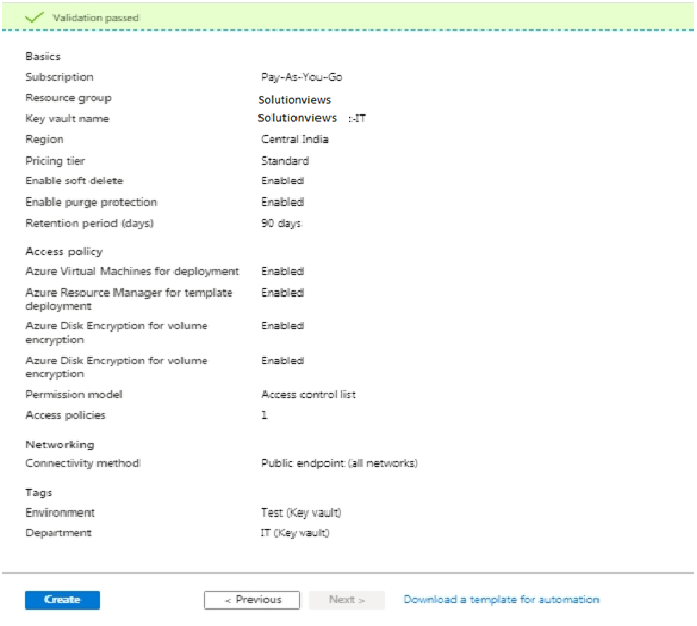
Click Review and Create.
Now, click on Create.
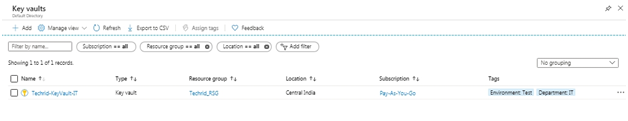
With your Resource Groups, Location &Tags you have created a Key Vault.

Click on Name. Here name is SolutionViews-KeyVault-IT.
Now, click on Keys and then on Generate/Import.
Now here, enter details and create a Key.
By default, the activation date will be set to the current date and the expiration date will be set to 2 years from the current date. It is changeable so you may change it if you want.
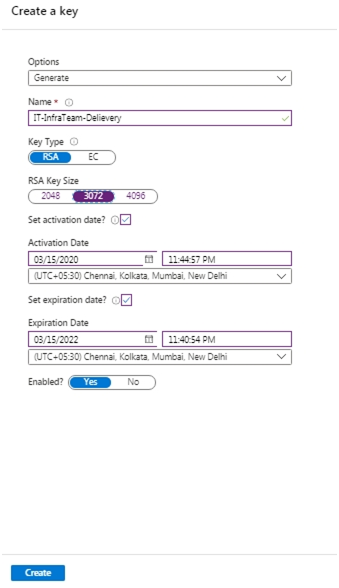
Click on Create.
The key is now created.
Creating Secrets.
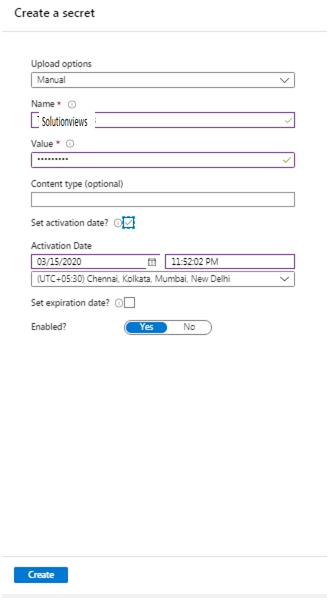
Click on Secrets and then on Generate/Import. Enter the data.
Secrets are now created.
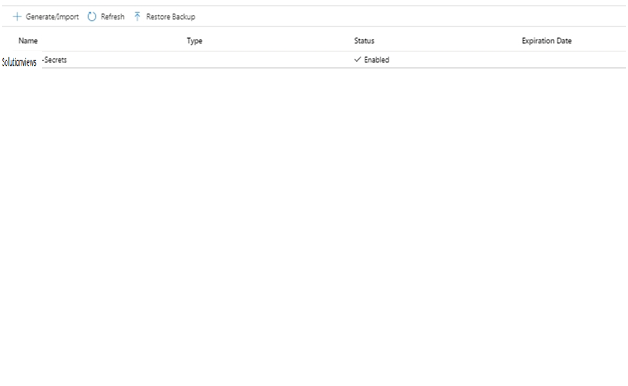
If anyone wants to view the Secrets and Tag applications to this secret, Click on Name Secrets.
Click on Tag and Assign.
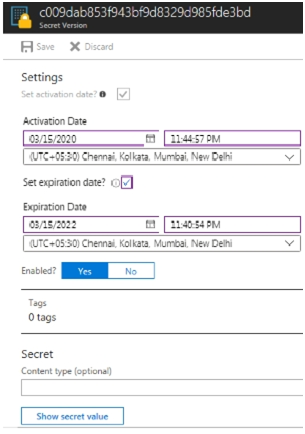
If you want to view Secrets, click on Show Secret Value.
Moving Key Vault to another subscription and Resource Group
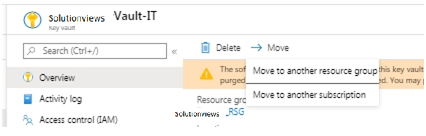
To move Key Vault to another subscription and Resource Group, click on Move.
NOTE: Before you perform this movement, ensure to have a resource group to place this Key Vault. No associated scripts will work until new resource IDs are updated.