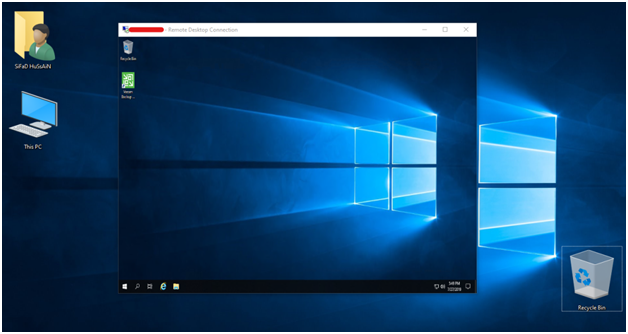
In the United Arab Emirates, I’ve had numerous instances of Remote Desktop connections failing. When our clients tried to remote into machines they had previously connected to successfully for a long time, they received error messages like this, so I fixed the problem last week.
Introduction:
The difficulty is Microsoft launched protection replacement to deal with vulnerabilities for the Credential Security Support Provider protocol (CredSSP) utilized by Remote Desktop Protocol (RDP) connections for Windows customers and Windows Server. You will face the CredSSP encryption oracle remediation blunders when you have programs or offerings inclusive of the Remote Desktop Connection that use CredSSP on an up-to-date machine.
Important: CredSSP is an authentication issuer that approaches authentication requests for different applications. any software which relies upon CredSSP for authentication can be prone to this kind of attack Once you’ve got mounted the patch on a “vulnerable” pc and try and hook up with an unpatched server, you’ll see the subsequent blunders message that occurs once you into your password to authenticate to the RDP session.
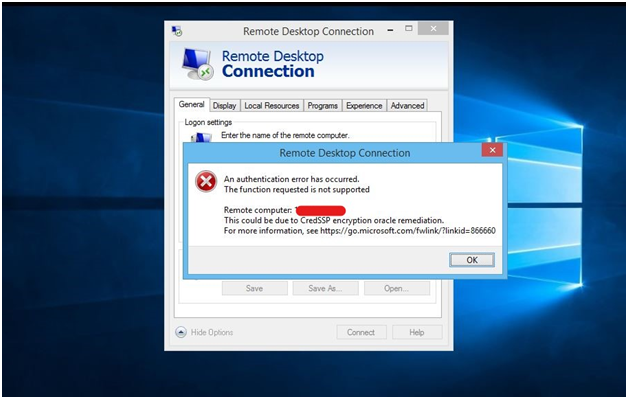
Specifically a vulnerability within the Windows subsystem, Credential Security Support Provider protocol (CredSSP). This vulnerability applies to all present-day variations of Windows Operating systems and permits for a far-flung code execution vulnerability. However, post patching this triggered trouble wherein the patched customers have been blocked from communicating with unpatched servers over RDP protocols. Let’s check Windows RDP CredSSP encryption oracle remediation blunders fix.
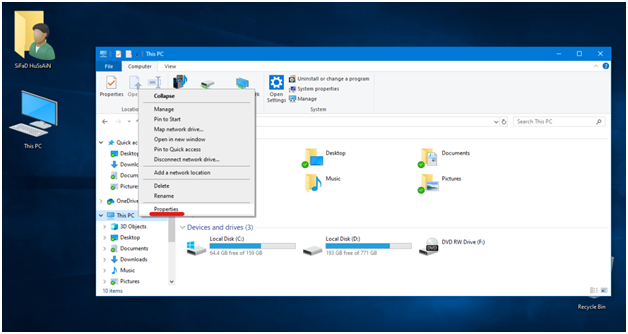
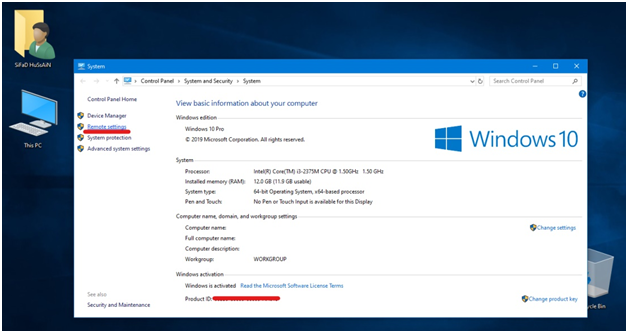
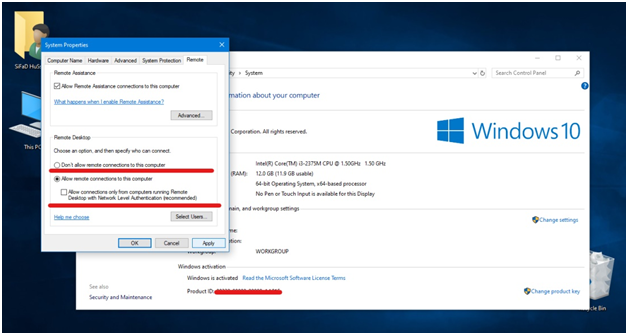
- Adjust the security setting to lower level from remote security setting. Click the file explorer in top left corner choose computer and then its properties by clicking right. Choose properties and then change and access remote tab.
Important: Deactivate the option “Allow connections only from computers running Remote Desktop with Network Level Authentication” (it’s suggested)
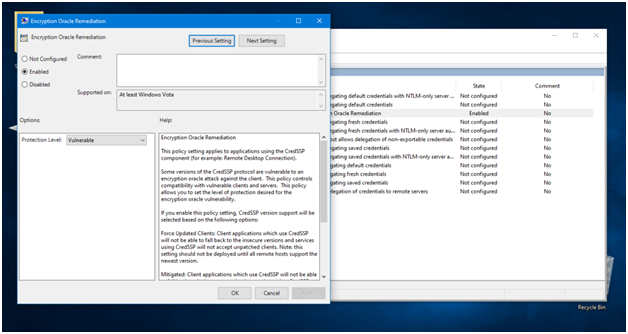
- To make changes in group policy enter run gpedit.msc then enter group policy and select edit group policy.
3- Use the following steps:
1st computer configuration
2nd administrative templates
3rd system
4th credential delegation
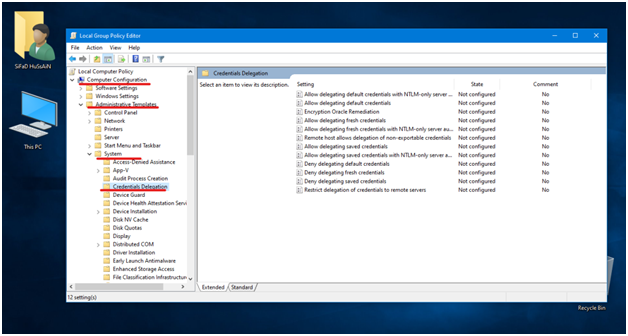
4- From the right pane choose encryption oracle remediation (its absence indicates that your machine is unpatched.)
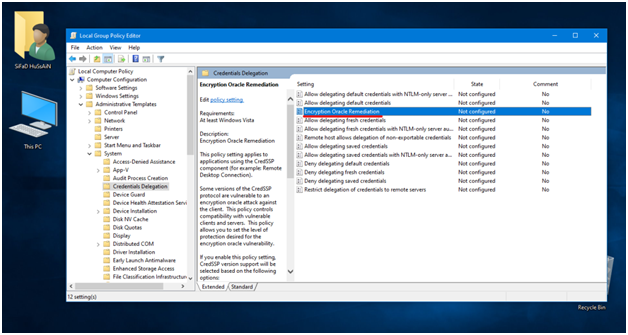
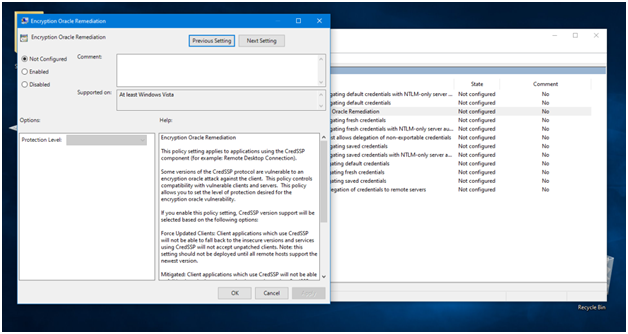
5- Alter this setting “encryption oracle remediation
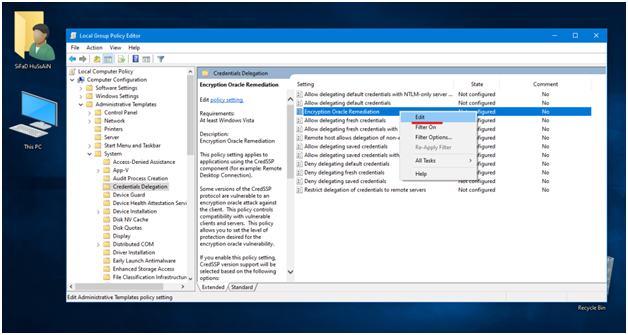
6- save the security level to vulnerable and set it to enabled.
CredSSP Encryption Oracle Remediation Policy Settings
There are 3 policy-setting available that can be activated.
- Force update clients
The highest level of security is force update clients. But it requires applying updates to all the customers you are transacting data with using credSSP so do not select or activate it till you apply updates to all members.
- Mitigated
The application remote desktop connection is blocked by this application if the server is not updated. Only those servers will work which have CredSSP.
- Vulnerable
The lowest level of security is vulnerable. It allows any server to connect using RDP but also allows the servers to attack.
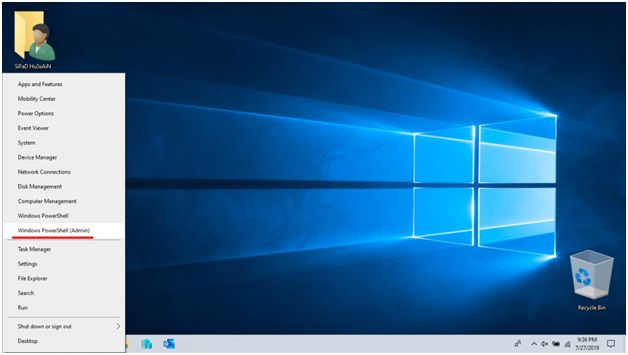
7- Press right-click select start and then select windows power shell.
8- Type the following command in the window power shell and enter
Gupdate/force
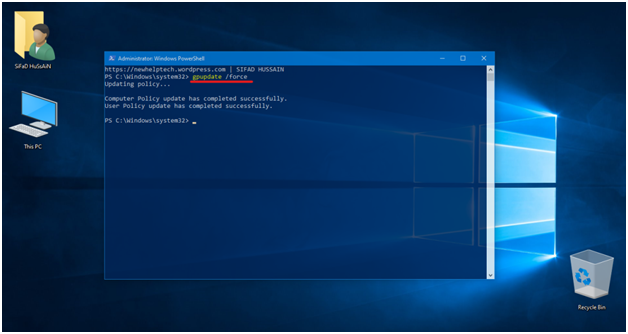
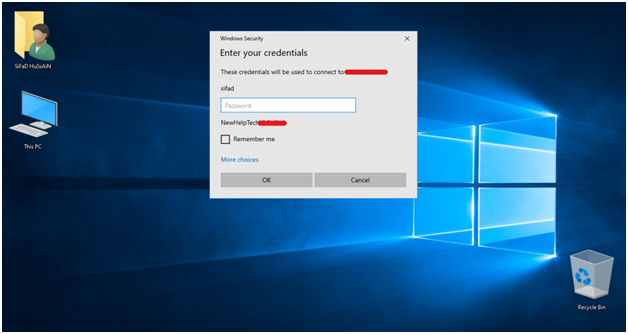
9- Now using RDP try to connect to other server. You will connect successfully.
CredSSP Encryption Oracle Remediation Registry Setting
You can also set the policy set by registry and a reboot
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System\CredSSP\Parameters] “AllowEncryptionOracle”=dword:00000002