When you create a domain, by default all FSMO roles are assigned to the first domain controller in the forest. You can transfer FSMO roles from one DC to another using both the Active Directory graphics snap-ins and the PowerShell command prompt.
There are several tools to manage FSMO roles in an AD domain: MMC snap-ins, Ntdsutil.exe command-line utility, and PowerShell. In our opinion, PowerShell is the most convenient way to manage AD FSMO roles today. The only drawbacks are the unusual syntax. Otherwise, there are only positive things, PowerShell allows you to transfer, or seize roles with just one command.
There are five FSMO roles
- Schema Master
- Domain Naming Master
- PDC
- RID pool Master
- Infrastructure Master
Transfer FSMO roles using PowerShell cmdlets from the Active Directory PowerShell module has the following benefits:
- You do not need to connect with the MMC snap-ins to the future role owner;
- Transferring or seizing FSMO roles does not require a connection to the current or future role owner. You can run AD-PowerShell module cmdlets on a Windows 10 desktop client or
- an amber server running Windows Server (with the RSAT package installed);
- To seize the FSMO role (if the current owner is not available), use the additional -force parameter.
Import Active Directory module to the current PowerShell session:
Import-Module activedActiveDirectory
Tip: Windows Server 2012 or later, the Active Directory module for PowerShell is loaded by default.
To get the forest level FSMO role holders in the specified domain (Domain Naming Master and Schema Master roles) use the following PowerShell command:
Get-ADForest contoso.com| ft DomainNamingMaster, SchemaMaster
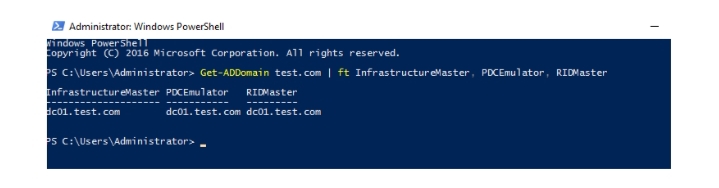
To view domain-wide FSMO role owners (Infrastructure Master, PDC Emulator, and Relative Identifier Master roles):
Get-ADDomain contoso.com | ft InfrastructureMaster, PDCEmulator, RIDMaster
Or you can get information about all roles in your AD using the following PowerShell one-liner:
et-ADDomainController -Filter * | Select-Object Name, Domain, Forest, OperationMasterRoles | Where-Object {$_.OperationMasterRoles}
Transfer FSMO Roles Using PowerShell
To transfer FSMO roles between Active Directory domain controllers use the PowerShell cmdlet Move-ADDirectoryServerOperationMasterRole.
To use the Move-ADDirectoryServerOperationMasterRole cmdlet, your environment must meet the following requirements:
- There must be at least one domain controller with a version of Windows Server 2008 R2 or newer;
- Installed PowerShell 3.0 or newer;
- Imported Active Directory module (2.0 or newer).
Check the current Active Directory schema version:
Get-ADObject (Get-ADRootDSE).schemaNamingContext -Property object
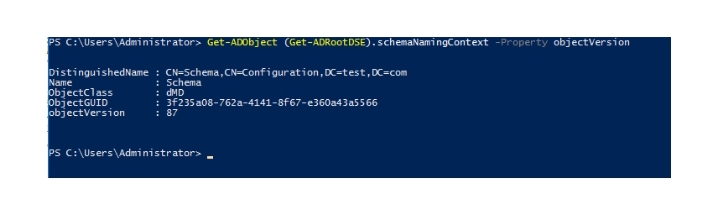
In this case, the AD object version is 87. This corresponds to the version of the AD schema in Windows Server 2016, so we can transfer the FSMO roles from PowerShell.
Unlike the Ntdsutil.exe utility, the Move-ADDirectoryServerOperationMasteRole cmdlet can be performed from any domain computer.
Note. To migrate the Operations Master roles, your account must be a member of privileged domain groups: Domain admins and Enterprise Admins.
For example, to transfer the PDC Emulator role to a domain controller named dc2, use the command:
Move-ADDirectoryServerOperationMasterRole -Identity “dc2” PDCEmulator
You can run this command on any domain controller, including one that is neither the old nor the new role holder.
It is possible to transfer several roles at once:
Move-ADDirectoryServerOperationMasterRole -Identity “dc2” –OperationMasterRole DomainNamingMaster,PDCEmulator,RIDMaster,SchemaMaster,InfrastructureMaster
Tip. To simplify the Move-ADDirectoryServerOperationMasterRole cmdlet usage, you can replace the names of roles with numbers from 0 to 4. The correspondence of names and numbers is given in the following table:
PDCEmulator 0
RIDMaster 1
InfrastructureMaster 2
SchemaMaster 3
DomainNamingMaster 4
Thus, the last command can be replaced by a shorter one:
Move-ADDirectoryServerOperationMasterRole “dc2” –OperationMasterRole 0,1,2,3,4
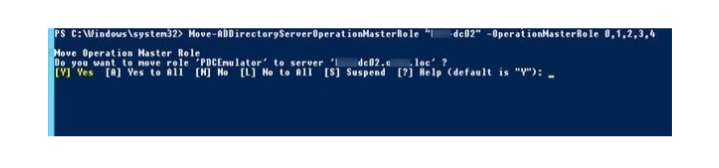
Do you want to move role ‘PDCEmulator’ to server ‘dc2.theitbros.lock?
[Y] Yes [A] Yes to All [N] No [L] No to All [S] Suspend [?] Help (default is “Y”): A
After entering the FSMO transfer command for all or several roles, a prompt appears asking whether you want to confirm your actions or cancel them. To transfer all roles press A > Enter. To skip confirmation, you can add the -Confirm:$false parameter to the previous command.
If you want to execute the FSMO transfer command under another user account, you can use the -Credential parameter:
$cred = Get-Credential
Move-ADDirectoryServerOperationMasterRole -OperationMasterRole SchemaMaster -Identity AD -Verbose -Force -Credential $cred
Seizing FSMO Roles Using PowerShell
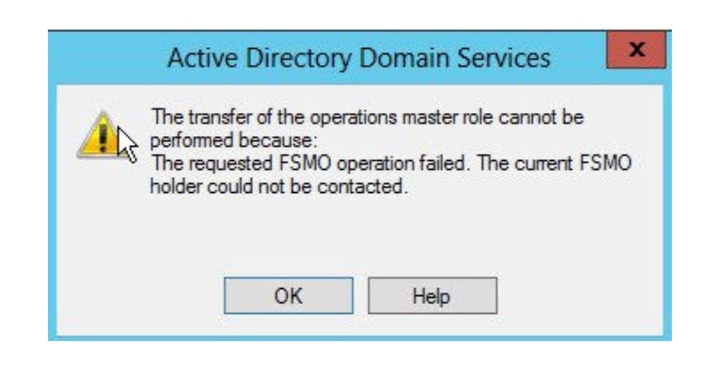
If the current owner of one or all of the FSMO roles fails, you can receive the following error when trying to use the Move-ADDirectoryServerOperationMasterRole cmdlet:
Move-ADDirectoryServerOperationMasterRole: The directory service is unavailable
In this case, you can force the transfer (seize) of FSMO roles using the -Force option:
Move-ADDirectoryServerOperationMasterRole -Identity “dc2” –OperationMasterRole DomainNamingMaster,PDCEmulator,RIDMaster,SchemaMaster,InfrastructureMaster –Force
Use the –force parameter when you face the error when moving the FSMO roles using the graphical snap-ins:
The transfer of the operation master role cannot be performed because The requested FSMO operation failed. The current FSMO role holder could not be contacted.
When transferring or seizing the FSMO roles, keep in mind the following restrictions:
- Do not assign the Infrastructure Master role to a domain controller that is a Global Catalog server, as it won’t update object information in the domain. The reason for this behavior is that the global catalog server maintains partial replicas of all objects in the forest;
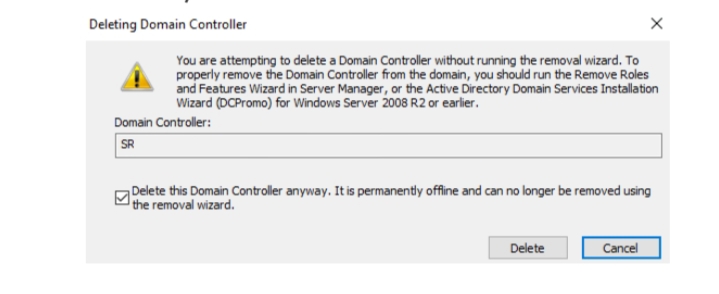
- After the FSMO roles have been seized, the domain controller from which the roles were seized should never be connected to the domain (don’t forget to remove this DC computer account from the domain using the ADUC snap-in).
As you can see, PowerShell allows you to perform FSMO role management tasks much faster and easier than the Ntdsutil tools and the MMC snap-ins.